When public key systems are used for identification, the private key is used to create a signature and the public key is used to verify that signature. … Public key cryptography can be used for either offline authentication or online authentication.
How public key cryptography can be used for identification?
When public key systems are used for identification, the private key is used to create a signature and the public key is used to verify that signature. … Public key cryptography can be used for either offline authentication or online authentication.
How public key cryptography is used for digital signature?
Digital signatures are based on public key cryptography, also known as asymmetric cryptography. Using a public key algorithm, such as RSA (Rivest-Shamir-Adleman), two keys are generated, creating a mathematically linked pair of keys, one private and one public. … This is how digital signatures are authenticated.
Where is public key cryptography used?
The public key is used to encrypt plaintext or to verify a digital signature, whereas the private key is used to decrypt ciphertext or to create a digital signature. Messages encrypted with a public key can only be decrypted using the same private key pair.What 2 use cases can public key cryptography be used for?
In addition to being used to encrypt messages, key pairs can be used for digital signatures and document signing. Public key cryptography uses the sender’s private key to verify a digital identity.
What are the three ways public key encryption can be used?
This process now exists and is an integral part of Public Key Cryptography. Public key cryptography involves two keys: a private key that can be used to encrypt, decrypt, and digitally sign files, and a public key that can be used to encrypt and a verify digital signatures.
How does cryptography verify identity?
- a trusted list of central certificate authorities like in HTTPS.
- key-signing parties where people validate and sign each other’s keys in person, like used with the OpenPGP Web of Trust.
How does public key cryptography provide integrity?
Public key encryption is a much slower alternative to symmetric cryptography. … Authentication is provided by taking a piece of text, encrypting it using the private key which is only known by you. If it can be decrypted using your public key, then it is known to be encrypted by you.What is a public key and how is it used?
In cryptography, a public key is a large numerical value that is used to encrypt data. The key can be generated by a software program, but more often, it is provided by a trusted, designated authority and made available to everyone through a publicly accessible repository or directory.
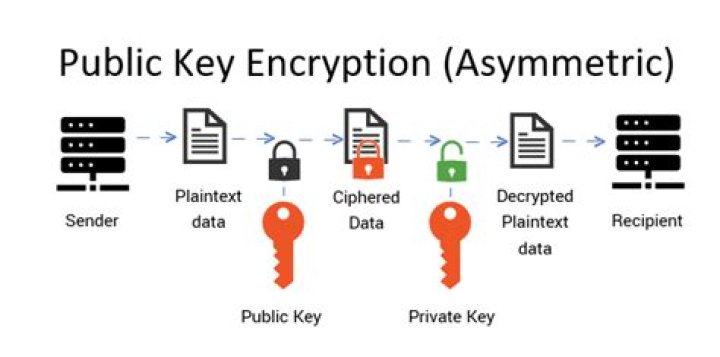
What is the concept of public key cryptography?Public key cryptography (PKC) is an encryption technique that uses a paired public and private key (or asymmetric key) algorithm for secure data communication. A message sender uses a recipient’s public key to encrypt a message. To decrypt the sender’s message, only the recipient’s private key may be used.
Article first time published onHow public keys are distributed using public key authority?
In public key cryptography, the key distribution of public keys is done through public key servers. When a person creates a key-pair, they keep one key private and the other, known as the public-key, is uploaded to a server where it can be accessed by anyone to send the user a private, encrypted, message…
What is difference between public key cryptography and digital signature?
3 Answers. Digital signatures use public key cryptography, so it’s not very clear what you’re asking. That being said, public key encryption by itself cannot be used for non-repudiation, so you’ll always want digital signatures, regardless of which one is faster.
What are the roles of the public key and private key in cryptography?
In Public key, two keys are used one key is used for encryption and another key is used for decryption. One key (public key) is used for encrypt the plain text to convert it into cipher text and another key (private key) is used by receiver to decrypt the cipher text to read the message.
Where is asymmetric cryptography used?
Asymmetric encryption is used in key exchange, email security, Web security, and other encryption systems that require key exchange over the public network. Two keys (public and private), private key cannot be derived for the public, so the public key can be freely distributed without confidentially being compromised.
How does public key and private key work?
In public key cryptography, every public key matches to only one private key. … Together, they are used to encrypt and decrypt messages. If you encode a message using a person’s public key, they can only decode it using their matching private key.
Which of the following process is used for verifying the identity of a user?
The process of verifying the identity of a user is called Authentication.
How do you implement identity verification?
- Knowledge-based authentication.
- Two-factor authentication.
- Credit bureau-based authentication.
- Database methods.
- Online verification.
What is the need of identity verification in cyber security?
Identity verification ensures that there is a real person behind a process and proves that they are who they claim to be. This prevents anyone from carrying out a process on other people’s behalf without authorisation, creating false identities, or committing fraud.
How many keys are used with public key cryptography?
Public key encryption uses two different keys. One key is used to encrypt the information and the other is used to decrypt the information. Sometimes this is referred to as asymmetric encryption because two keys are required to make the system and/or process work securely.
How does public key cryptography provide both sender authentication and confidentiality?
Instead of a single key, the public-key encryption system uses a pair of keys which are mathematically linked to each other–one of which is kept secret and the other which is transmitted. … Public-key encryption thus provides for both confidentiality and authentication. The benefits of public-key encryption are clear.
Which cryptography symmetric or public is used for message integrity How is it used?
The RSA algorithm allows people to use public and private keys to encrypt a message. When a public key is used for encryption, a private key will facilitate decryption and vice versa. Due to this property, it has become a popular asymmetric encryption algorithm.
How are public and private keys are used for confidentiality integrity and authenticity?
By using a public and private key for encryption and decryption, recipients can be confident that the data is what the sender says it is. The recipient is assured of the confidentiality, integrity and authenticity of the data. … The only way to decrypt Alice’s private key is with her public key, which Bob can access.
How does public key cryptography work quizlet?
How does public Key Encryption work? Mathematical Algorithms are used to create two separate keys for the encryption/decryption process. One key is private (used to decrypt) and the other is public (used to encrypt). You cannot decrypt the message using the key that was used to encrypt it.
What is used to store and distribute a public key?
A public key infrastructure (PKI) is a system for the creation, storage, and distribution of digital certificates which are used to verify that a particular public key belongs to a certain entity. … A certificate policy stating the PKI’s requirements concerning its procedures.
What is public key and private key in digital signature?
A public key, as the name implies, is openly available to anyone who wants it. … In asymmetric encryption, a public key and a private key are used. The sender’s private key encrypts the data — this is the digital signature — and the receiver uses the public key to decrypt it and verify it matches the attachment.
Is digital signature scheme possible without public key cryptography?
Since digital signature is created by ‘private’ key of signer and no one else can have this key; the signer cannot repudiate signing the data in future.
What are the roles of the public key?
The public key is used to encrypt and a private key is used decrypt the data. The private key is shared between the sender and receiver of the encrypted sensitive information. The public key is also called asymmetric cryptography.
What is the purpose of cryptography and what are its applications?
Used in a variety of fields in the real world, cryptography uses encryption to hide information in a coded language that does not let adversaries (malicious third parties) access it anyhow. Simply put, cryptography prevents unauthorized access to information and keeps data secure and safe.
How public and private keys are used differently in asymmetric key cryptography and digital signature?
Asymmetric encryption uses a mathematically related pair of keys for encryption and decryption: a public key and a private key. If the public key is used for encryption, then the related private key is used for decryption. If the private key is used for encryption, then the related public key is used for decryption.
How does public key asymmetric encryption work?
Asymmetric Encryption, also known as Public-Key Cryptography, is an example of one type. Unlike “normal” (symmetric) encryption, Asymmetric Encryption encrypts and decrypts the data using two separate yet mathematically connected cryptographic keys. These keys are known as a ‘Public Key’ and a ‘Private Key.
Which type of cryptography uses only private keys?
Asymmetric Cryptography uses a shared private key only. Secret key cryptography, sometimes also called symmetric key, is widely used to keep data confidential. However, protecting one key creates a key management issue when everyone is using private keys.